What is Access Control & How does it help Potect Data
More than ever, the way we work must be flexible. Some companies keep several collaborators or all working from home or the location of their convenience. Those workgroups carry out their tasks both in an office or each from wherever they are. However, we must take care of who must access both data and system resources. This guide will explain everything you need to know regarding access control, its most common variants, and a fairly reliable solution to start implementing it as soon as possible.
What is access control?
It is a method to ensure that users prove to be who they say they are. It’s like when you have to show your identity document somewhere to verify that you have that identity. Access control is extremely important so that all users have corresponding access to data and system resources. Now, what is access control specifically? More than anything, in a series of restrictions that are applied according to the data and resources to which you want to access. It is based on authentication and authorization processes.
If we talk about authentication, we do it with regard to entering credentials or using one or more authentication methods. On the other hand, authorization is the sequential step of authentication, which grants access to a certain group of resources and data.
Access control types
We list below the most common types of access control, that is, the ones that have been most implemented so far. According to the needs of your company or workgroup, you can choose one or the other option.
Role-Based Access Control (RBAC)
It can be said that this type of access control is one of the most used. It is based on granting access to users based on assigned roles. In addition, and to add extra layers of protection, security policies are applied that limit the obtaining of privileges. These privileges can be applied to both data access and system resources. Today, privilege escalation is an internal corporate threat that wreaks havoc. The great level of damage, especially at an economic level that it generates, should be a point of attention for any company susceptible to this type of security threats.
Discretionary Access Control (DAC)
It is a type of access control that dictates that the data owner decides on the accesses. This means that these accesses will be granted to users based on the rules that the owner of the data himself specifies.
Mandatory Access Control (MAC)
This variant can be considered as somewhat more arbitrary than the others. This is so in the sense that users are granted access based on regulations established by a central authority in a company or some other regulatory organization.
Attribute-Based Access Control (ABAC)
The distinction of this type of access control is that a series of attributes are added to the user and the resources to which access corresponds. They allow evaluations to be made that indicate the day, time, location, and other data. All of this is taken into account when granting or limiting access to data and resources. This is a type that applies a more dynamic method that adapts to users’ situation to have more or less access.
Also Read: Benefits of Using HMA VPN
What type of access control is more convenient?
One of the aspects that guarantee the correct implementation of any access methods is to comply with the rules, regulations, and standards. Depending on the country in which you are located, you may need to review in detail regulations such as GDPR, which would be a personal data protection policy that is valid for all of Europe. Another important example is the PCI-DSS, a regulation responsible for securing and protecting both transactions and data of credit and debit cardholders. According to each norm, regulation, or standards, all kinds of sanctions can be applied if compliance is neglected.
Why do we mention this? More than anything because there is no one method that is strictly more convenient than another. Each work environment has specific needs. Likewise, it is good to keep in mind that the most modern and recent types of access control are based on attributes. It is especially convenient because permissions are granted or limited according to the user’s current situation. For example, if you change the location or device. However, one thing that should not be negotiated is compliance.
Azure Active Directory: the IAM that’s everywhere
You may wonder what is the ideal solution to implement access control. There is precisely no one-size-fits-all, all-powerful solution. There may be scenarios where you need one or more technologies at once to meet your access control needs.
A large part of work environments uses Microsoft and its associated applications. Microsoft Azure Active Directory offers smart access policies. In this way, all work resources will be protected and accessible only by those who need it. According to the requirements, you can have the Azure Active Directory solution by itself or, if you already use Microsoft services such as Office 365, you can opt for the integration. The latter is much faster to implement.
This solution, which is part of the Azure suite, is one of the most popular and functional companies. Above all, those that are very large, such as multinationals. Mainly because it has the ability to be in control and manage not just tens but hundreds, thousands, or millions of users. It allows the creation of unique administration credentials so that each collaborator of a company or workgroup can have access to the diverse resources in the cloud already implemented. This even applies to those people who use operating systems other than Windows.
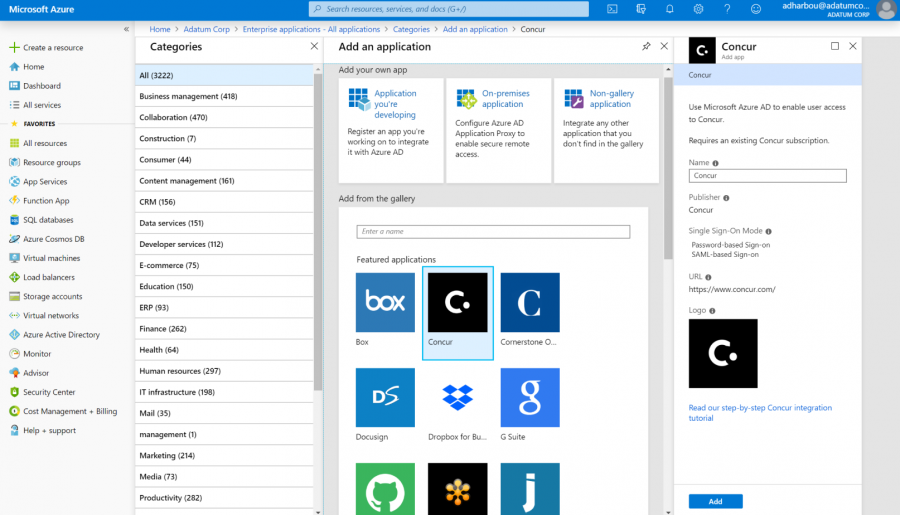
An interesting advantage is that the entire work environment under the Azure Active Directory is secure, even if the membership includes people from outside the company or collaborators / temporary members. One of the challenges of shared work environments is that outsiders have improper access to data or system resources that contain sensitive or confidential content.
On the other hand, if you prefer, you can adapt the user interface as you prefer so that it can be adapted to the image of your company or workgroup as you prefer.
Key features of Azure Active Directory
- User and workgroup management
- Authentication with the SSO method (Single Sign-On)
- Multi-Factor Authentication
- B2B (Business-to-Business) collaboration
- Password management through a Self-Service portal
- Synchronization Engine
- Registration of devices used by users
- Security Reports and Use of AAD services
We have commented that it supports devices that can use operating systems other than Microsoft. We quote them below:
- Any Windows computer or tablet
- Android devices
- iPhone or iPad
- Devices that have the macOS system (Macbook, iMac)
- Any web-based device (Chromecast, for example)
In case you want to start testing, keep in mind that you have a free plan with limited functionalities but ideal for beginners. Later, you can switch to the payment plans with the annual payment method. You can enter the following link for more information.